RegreSSHion & Internet Facing Servers
Vulnerability reintroduced to SSH exposes 14millions servers to critical attack vector

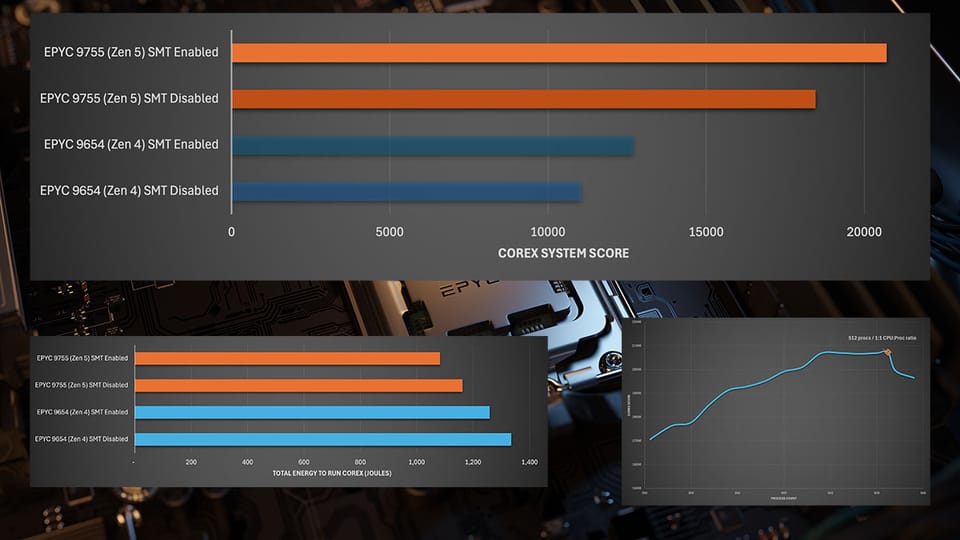
14million. That’s the estimate by Qualys of the number of servers potentially vulnerable to CVE 2024-6387 aka regreSSHion that are “exposed to the internet”.
That seems like a lot of machines to me. I’m not a security specialist and while we do a little work for some of our smaller clients that involves internet facing services the bulk of what we do is on private corporate networks. I’m not the best person to comment on this, I accept that.
But still. I’m still a little surprised at the number of machines that would have a valid use case for having an SSH daemon process exposed to the internet. Or have I just misunderstood the statement by Qualys?
Whenever we design systems, HPC or not, cloud or on-prem, large scale enterprise or early stage startup, access to everything is designed to be at the lowest possible level. Servers do not have SSH daemon port exposed to any public networks. That sort of access is always via another level of indirection. A bastion host, a jumpbox, via a corporate secure link.
Oh and you write a test case for every bug you fix so they’re not regressed right? (Yea I know race conditions are kind of a pain/impossible to do… )
Threat Report from Qualys

14 million servers